Agent Deployments
Scale Your Business.
Your team is building with agents — deploying them into workflows, connecting them to tools, and scaling them across your organization. Interchange is the infrastructure layer that makes all of it manageable.
Interchange gives your team full visibility and control over every agent action — so you can move fast with confidence.
The problems keeping your team up at night.
“It's the Wild West”
Your agents are operating on best efforts. No standard policies. No enforcement. Just trust.
Interchange enforces policies at the protocol level.
“My compliance team can't sleep”
Every agent action is a potential audit finding, and right now there's no trail to follow.
Every action is logged with cryptographic proof.
“What if it sends messages to investors?”
One unauthorized agent action could mean regulatory disaster. You have no way to stop it in advance.
Permission boundaries that hold up under audit.
“People are losing tens of thousands”
Runaway agents with no spending limits are burning cash overnight. No alerts, no caps, no control.
Real-time monitoring with enforceable limits.
The operating system for your agent workforce.
Deploy, manage, and scale agents with full visibility at every step.
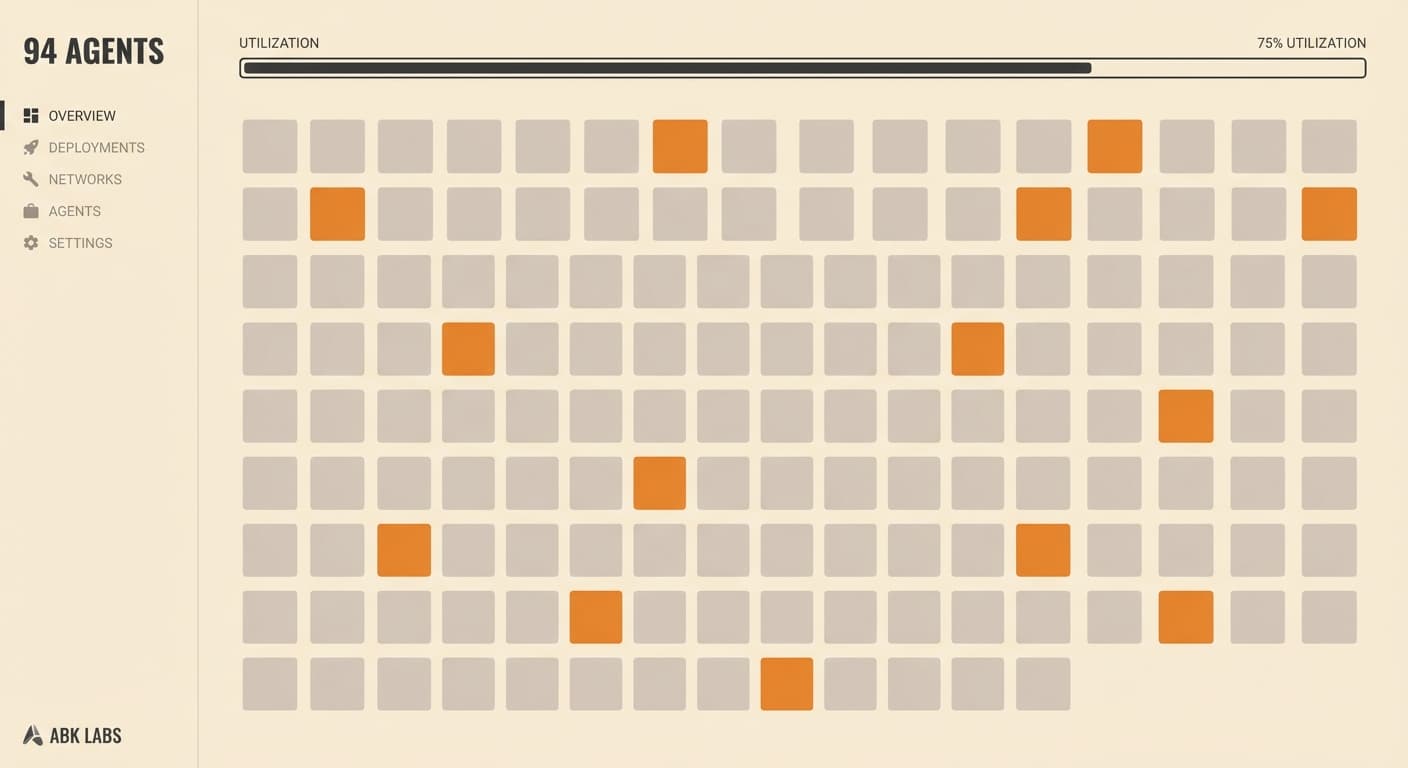
Scale without rebuilding
Go from 1 agent to 100 without rearchitecting your controls. Identity, governance, and audit trails that grow with you.
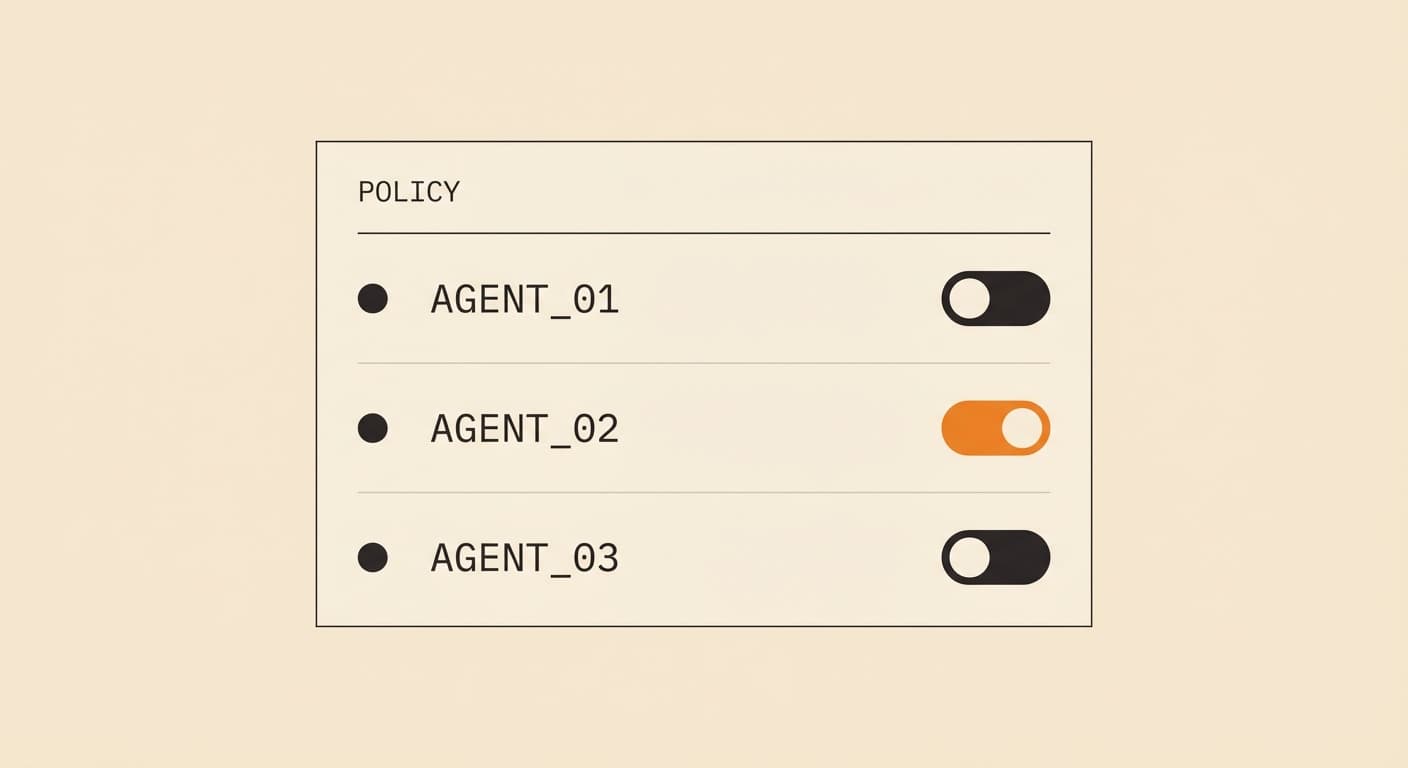
Govern every agent
Define permissions once, enforce them everywhere. Protocol-level policies for what each agent can access, spend, and do.
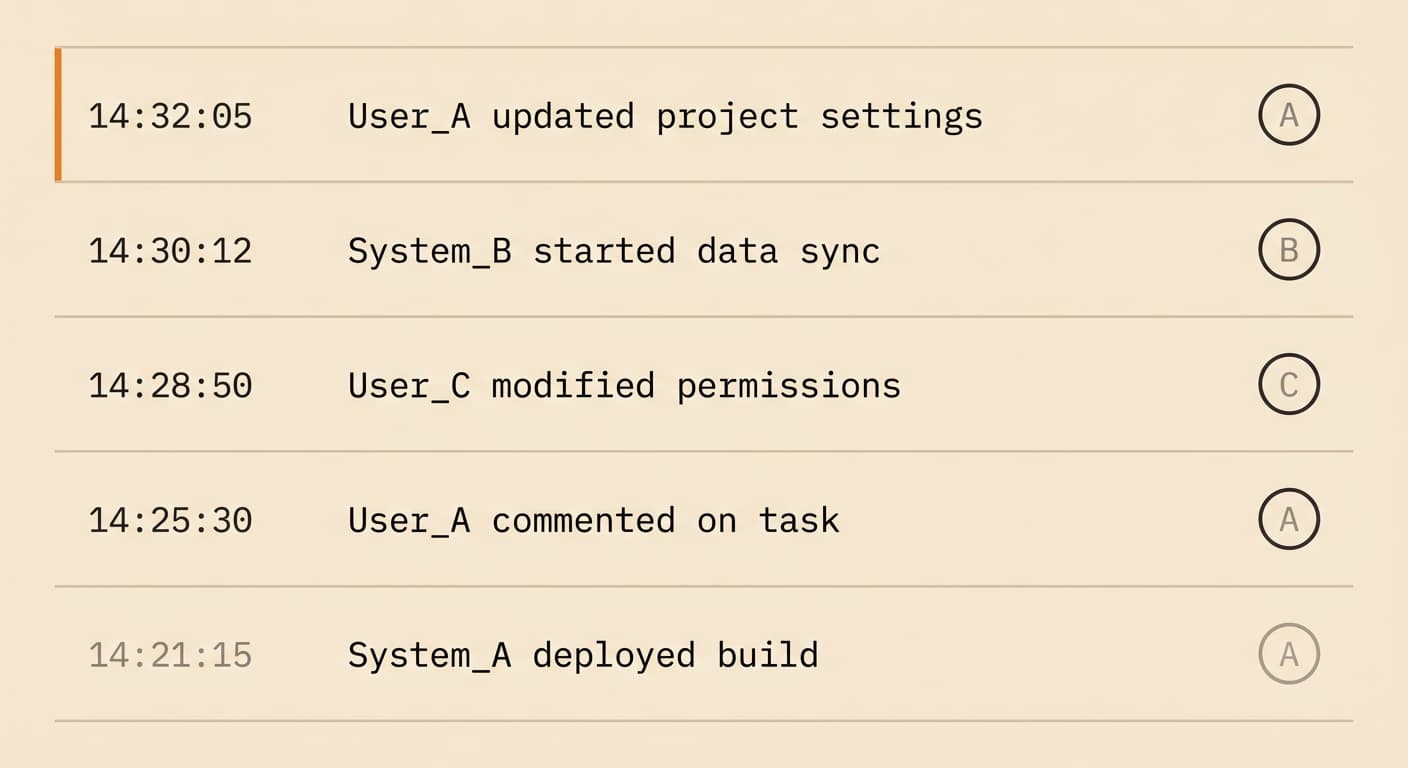
See everything in real time
Every agent action logged with a cryptographic identity attached. One dashboard across your entire organization.

Prove it to regulators
Immutable, timestamped audit trails for every action. Export-ready for SEC, NFA, or internal compliance reviews.
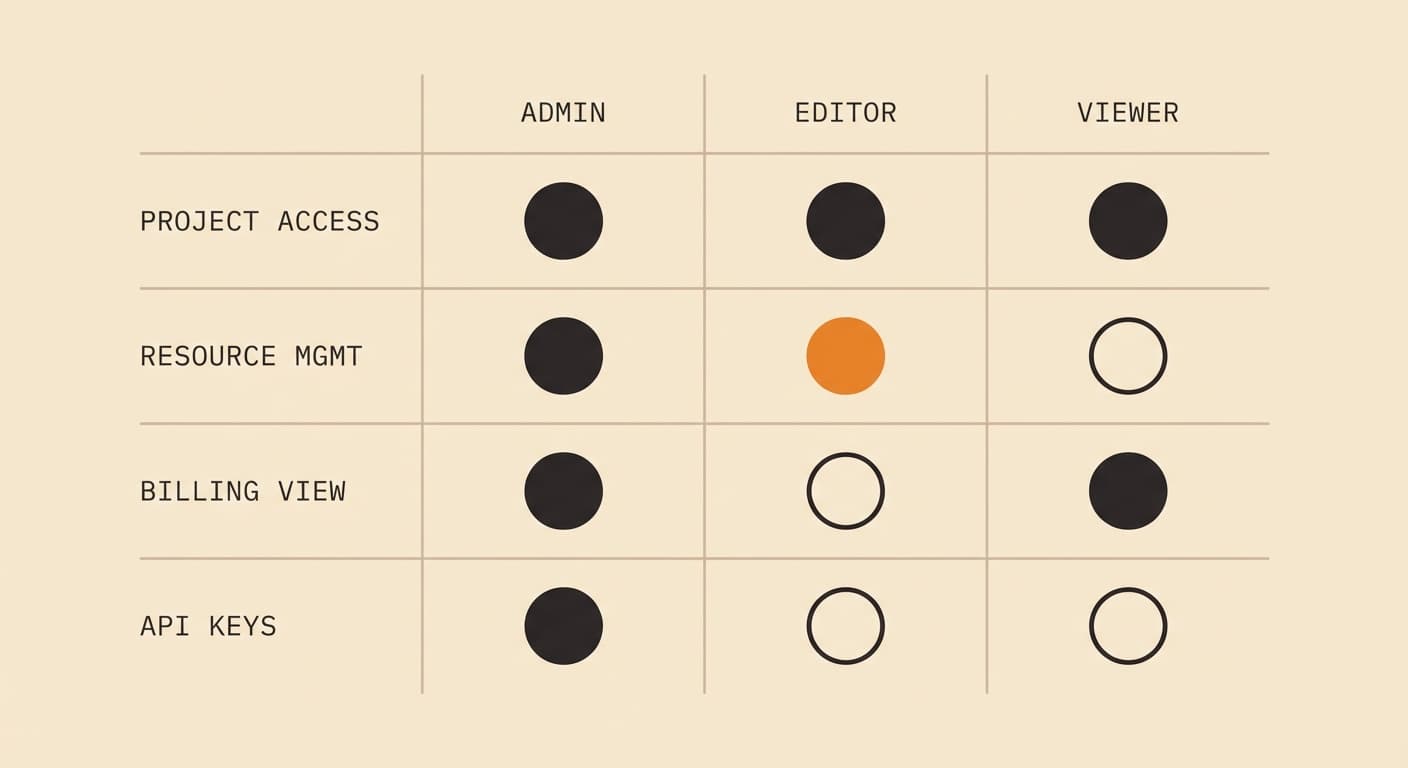
Control access across teams
Role-based permissions scoped by team, function, or budget. Add teammates, revoke access instantly, set spending limits that stick.
See everything
Full visibility into every agent, every action, every connection. No gaps, no guesswork.
Control everything
Set policies that enforce themselves. No manual intervention required. Boundaries that hold.
Prove everything
Cryptographic audit trail that satisfies any regulator or auditor. Export on demand.
Put your agents
to work.
Deploy your first agent in minutes. See every action it takes. Scale to hundreds when you’re ready.
Book a Call